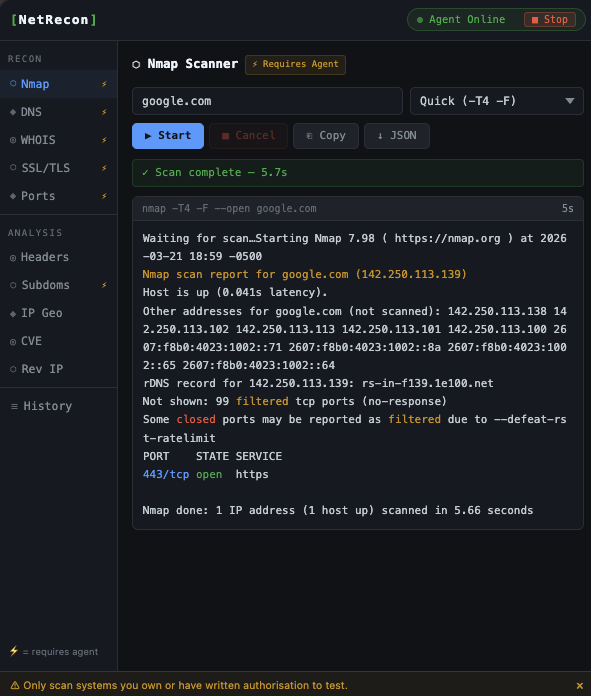
// CHROME EXTENSION · MV3 · SIDE PANEL
10 security tools.
One side panel.
NetRecon is a browser-based security toolkit for pentesters, sysadmins, and security researchers. Nmap scanning, DNS recon, WHOIS, SSL inspection, port scanning, CVE lookup, subdomain enumeration, and more — all without leaving your browser.
Free · No account · Chrome MV3 · Requires Node.js companion server
⚠ For authorized testing only